Things the guys who stole my phone have texted me to try to get me to unlock it - Gothamist
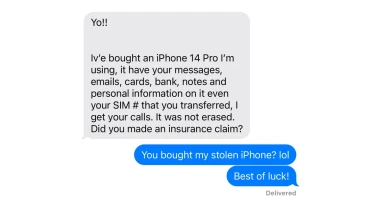
This is a very entertaining and educational article, giving insights into the methods used by thiefs to try and get access to your phone data.
I don’t like Apple but it’s great that their security is so good when it comes to this.