Shadow Gambit: The Cursed Crew developer announces closure (www.eurogamer.net)

There have been multiple accounts created with the sole purpose of posting advertisement posts or replies containing unsolicited advertising.
Accounts which solely post advertisements, or persistently post them may be terminated.


The junta in Niger has ordered its armed forces to go on highest alert, citing an increased threat of attack, according to an internal document issued by its defence chief on Friday that a security source in the country confirmed was authentic.

Hands On: youtu.be/7XsXNw8vZFo?si=c48GYX5CkjLGtc56




The paper of record pokes holes in the absorb-everything AI business model.

Faced with new legislation, Iowa's Mason City Community School District asked ChatGPT if certain books 'contain a description or depiction of a sex act.'

Exploring the internals of Linux v0.01
Archived version: archive.ph/2Y3u6...



Devon O’Brien, technical program manager for Chrome security, explained on Thursday that starting in Chrome 116 – due August 15 – Google’s browser will include support for X25519Kyber768, an alphanumeric salad that desperately needs a catchy name....

Johnson & Johnson said on Thursday the U.S. Food and Drug Administration had approved its antibody-based therapy for patients with a difficult-to-treat type of blood cancer.






Kenya was hailed for its decision to outlaw single use plastic bags in 2016, with remarkably hefty penalties. So why are the bags back in stores, piling up in dumps — and being ingested by livestock?

I'm too tired now to give a nice explanation, but probably playing with Legos with my dad as a kid. Either that or waking up on a REALLY stormy summer morning and going to grandma's house.
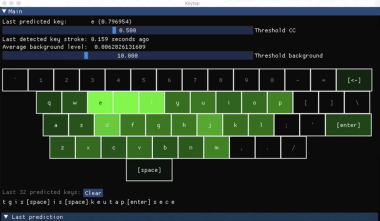
“Downfall attacks targets a critical weakness found in billions of modern processors used in personal and cloud computers. This vulnerability, identified as CVE-2022-40982, enables a user to access and steal data from other users who share the same computer. For instance, a malicious app obtained from an app store could use...