Port Fowarding minecraft server hardening question (gentoo)
So i’ve been hosting a modded Minecraft server for my friends and me on weekends. While it’s been a blast, I’ve noticed that our current setup using LAN has its limitations. My friends have been eagerly waiting for their next “fix” (i.e., when they can get back online), and I’ve been replying with a consistent answer: this Friday.
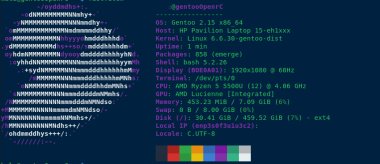
However, exploring cloud providers to spin up a replica of my beloved “Dog Town” Server was a costly endeavor, at least for a setup that’s close to my current configuration. As a result, I’ve turned my attention to self-hosting a Minecraft server on my local network and configuring port forwarding.
To harden my server, I’ve implemented the following measures:
- Added ufw (Uncomplicated Firewall) for enhanced security.
- Blocked all SSH connections except for the IP addresses of my main PC and LAN rig.
- Enabled SSH public key authentication only.
- Rebuilt all packages using a hardened GCC compiler.
- Disabled root access via
/etc/passwd. - Created two users: one with sudo privileges, allowing full access; the other with limited permissions to run a specific script (
./run.sh) for starting the server.
Additionally, I’ve set up a fcron job (a job scheduler) as disabled root, which synchronizes my Minecraft server with four folders at the following intervals: 1 hour, 30 minutes, 10 minutes, and 1 day. This ensures that any mods we use are properly synced in case of issues.
https://sh.itjust.works/pictrs/image/bae5a332-c374-41db-aaeb-e5da72c7f614.png
any suggestions of making the computer any more secure, aswell as backup solutions? thanks!
–added note, what hostnames do you guys call your servers? I used my favorite band albums and singles for hostnames.