Amazon’s $1.4B iRobot deal is dead. Now what? | TechCrunch (techcrunch.com)

There have been multiple accounts created with the sole purpose of posting advertisement posts or replies containing unsolicited advertising.
Accounts which solely post advertisements, or persistently post them may be terminated.
This magazine is from a federated server and may be incomplete. Browse more on the original instance.


A video about disposable vapes, and how addiction became the goal of every single company on the planet.

The chairs of two U.S. House committees asked the Biden administration to investigate four Chinese companies they say are involved in Ford Motor’s (F.N), opens new tab planned Michigan battery plant, according to a letter....

Does anyone here have a BOOX e-paper tablet? I’m a big fan of e-paper devices—I love my Pebble smartwatch, Kindle Paperwhite, and Light Phone II. I’ve been eyeing the Tab Ultra C for quite a while, and I am considering the pros and cons. Mostly, I intend to use it for browsing the web and maybe some light note taking and...

The solar and electric vehicle industries are critical for the world’s urgent transition away from fossil fuels. However, both industries source many of their critical inputs from the Uyghur Region, a region where the Chinese government is systematically persecuting the native Uyghur, Turkic, and Muslim-majority peoples,...

There's also an alternate script if you want to talk with a Republican senator, and you don't feel they'll be swayed by the language in the linked site.


Sexually explicit AI-generated images of Taylor Swift have been circulating on X (formerly Twitter) over the last day in the latest example of the proliferation of AI-generated fake pornography and the challenge of stopping it from spreading....

Google continues to struggle with cybercriminals running malicious ads on its search platform to trick people into downloading booby-trapped copies of popular free software applications. The malicious ads, which appear above organic search results and often precede links to legitimate sources of the same software, can make...
Cozy Bear, classified by the United States federal government as advanced persistent threat APT29, is a Russian hacker group believed to be associated with one or more intelligence agencies of Russia. The Dutch General Intelligence and Security Service (AIVD) deduced from security camera footage that it is led by the Russian...

The cuts work out to roughly 8 percent of the overall Microsoft Gaming division that stands at around 22,000 employees in total.


Google is spoon-feeding fake “Shark Tank approved” weight loss gummy candies to innocent people — and making money doing it.


The issue affected Google Kubernetes Engine (GKE), a system used to deploy, scale and manage how applications are “containerized.” GKE — the tech giant’s implementation of the open-source Kubernetes project — is used widely in healthcare, education, retail and financial services for data processing as well as...

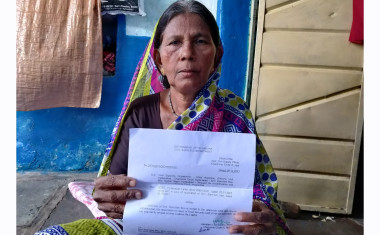
India runs one of the world’s largest food security programmes, which promises subsidised grains to about two-thirds of its 1.4 billion population....
Human Rights Watch interviewed dozens of LGBT people who indicated that they had reported being harassed, doxxed, outed, and abused on Facebook and Instagram, but in all these cases, Meta either did not respond to their complaints or found that the content they reported did not violate its policies, and the content remained...


I left the headline like the original, but I see this as a massive win for Apple. The device is ridiculously expensive, isn’t even on sale yet and already has 150 apps specifically designed for that....

Rob Miles has a Youtuber-style animation channel with a new video to communicate the importance of AI safety, and the execution is absolutely top notch.

Chinese state institutions issue rewards for finding the cybersecurity vulnerabilities in software that is often used by foreign governments, in what may be a subtle new form of state-backed cyber warfare. At the same time, China is promoting young cybersecurity engineers in a doubling of its efforts to probe foreign systems for...

His claims are quickly debunked in the article, as the true reason is, obviously, protecting their IP and subscription model
