Reddit’s deal with OpenAI will plug its posts into “ChatGPT and new products” (www.theverge.com)

There have been multiple accounts created with the sole purpose of posting advertisement posts or replies containing unsolicited advertising.
Accounts which solely post advertisements, or persistently post them may be terminated.
This magazine is from a federated server and may be incomplete. Browse more on the original instance.

Taiwan’s National Security Bureau (NSB) official Ko Cheng-heng said that Beijing’s campaign against Taiwan would spark a strong backlash from democracies around the world....


archive.ph/vlcmB

According to the European consumer protection group BEUC, the Chinese online retailer Temu “fails to provide sufficient traceability of the traders that sell on its platform” and thereby fail “to ensure that the products sold to EU consumers conform to EU law”, BEUC said in a release....
cross-posted from: lemy.lol/post/25062075

I was under the impression that Privacy Badger wasn’t considered useful any more . . . ? They should’ve just recommended using Firefox instead, yes?...


I’ve never completely understood this, but I think the answer would probably be “no,” although I’m not sure. Usually when I leave the house I turn off wifi and just use mobile data (this is a habit from my pre-VPN days), although I guess I should probably just keep it on since using strange Wi-Fi with a VPN is ok (unless...
Archive.org link...


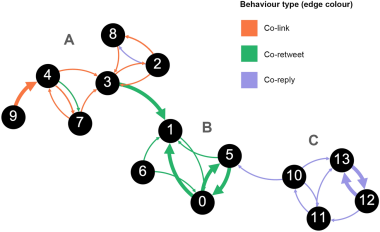
The authors introduce and evaluate an open-source software package and methodological framework for detecting and analysing coordinated behaviour on social media, namely the Coordination Network Toolkit, utilising weighted, directed multigraphs to capture intricate coordination dynamics....
I hate to go as cliche as “surprising absolutely no one,” but really, this is not a surprise.

This is the alternative Invidious link for the embedded article....

Canonical YouTube link


Archive link

A cyberattack on the Ascension health system operating in 19 states across the U.S. forced some of its 140 hospitals to divert ambulances, caused patients to postpone medical tests and blocked online access to patient records...

Archived link....


Archived version...
