Operation Triangulation - stealthy iOS malware (securelist.com)
Hell of an exploit chain, really interesting to dissect.

There have been multiple accounts created with the sole purpose of posting advertisement posts or replies containing unsolicited advertising.
Accounts which solely post advertisements, or persistently post them may be terminated.
This magazine is from a federated server and may be incomplete. Browse more on the original instance.
Hell of an exploit chain, really interesting to dissect.

I wondered how long this would take, and now we know.


Note: I am not affiliated with the project



Since this billionaire doesn’t want us to learn about what bad things he did, I figured we should let as many people know as possible:...


Archive Options Failing, Text Follows:...

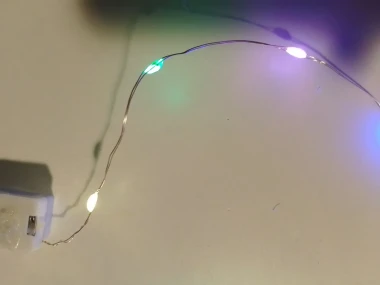
This was deeply silly and sort of made my day. Much more entertaining and funny that I expected from two hours of usb talk. Game show! This is a downer time of year for a lot of us so i hereby offer this little low stakes bright spot.



They dont look or feel isolated, like ones inside a headphone cable


Analysts have warned Windows 10 end of life plans could spark a global torrent of e-waste, with millions of devices expected to be scrapped in the coming years....

The original post uses "roll-up" instead of "catch-all" for some reason....


I’ve not done an in-depth look at this network but reading through their documentation shows it has a lot of similarity to the basics of the Nostr protocol and network. There is just not as much information available on the Polycentric site as there is already for Nostr. Nostr is also censorship resistant, with distributed...


archive.is/l66nX


