AI for identifying social norm violation (www.nature.com)
Prof. Yair Neuman and the engineer Yochai Cohen at Ben-Gurion University of the Negev have designed an AI system that identifies social norm violations. They trained a system to identify ten social emotions: competence, politeness, trust, discipline, caring, agreeableness, success, conformity, decency, and loyalty....

Installing Firefox... With Custom Profiles! (yewtu.be)
Link if you rather use YT: https://www.youtube.com/watch?v=OGC5CwEgr_g

The Secret Life of the 500+ Cables That Run the Internet (www.cnet.com)
These cables, only about as thick as a garden hose, are high-tech marvels. The fastest, the newly completed transatlantic cable called Amitié and funded by Meta, Microsoft and others, can carry 400 terabits of data per second. That’s 400,000 times faster than your home broadband if you’re lucky enough to have high-end...

Are you looking for chcpol003 assessment answers ?
As an AI language model, I do not have personal needs or goals, so I’m not “looking” for anything. However, I can certainly help you with information about the chcpol003 Assessment Answers , which is related to the unit of competency “Develop and Implement Policies.” Please note that providing specific answers to...
Copyright and why it's broken. - Tom Scott (www.youtube.com)
So recently there has been a lot of debate on AI-generated art and its copyright. I’ve read a lot of comments recently that made me think of this video and I want to highly encourage everyone to watch it, maybe even watch it again if you already viewed it. Watch it specifically with the question “If an AI did it, would it...

How to Move from Mastodon to Firefish (wedistribute.org)
Google’s nightmare “Web Integrity API” wants a DRM gatekeeper for the web (arstechnica.com)

Greg Rutkowski Was Removed From Stable Diffusion, But AI Artists Brought Him Back - Decrypt (decrypt.co)
Greg Rutkowski, a digital artist known for his surreal style, opposes AI art but his name and style have been frequently used by AI art generators without his consent. In response, Stable Diffusion removed his work from their dataset in version 2.0. However, the community has now created a tool to emulate Rutkowski’s style...

Instead of obtaining a warrant, the NSA would like to keep buying your data (arstechnica.com)

I Gazed Into Worldcoin’s Orb and Saw a Boring Dystopia Staring Back (gizmodo.com)
O R B

New vulnerability in SMS messaging could expose smartphone users' location to hackers, researcher says (arxiv.org)
Evangelos Bitsikas, who is pursuing a PhD in cybersecurity at the Northwestern University in the US, applied a new machine-learning program to data gleaned from the SMS system of mobile devices....

Study shows how images and sounds can be used for indirect prompt and instruction injection in multi-modal LLMs (arxiv.org)
An attacker generates an adversarial perturbation corresponding to the prompt and blends it into an image or audio recording. When the user asks the (unmodified, benign) model about the perturbed image or audio, the perturbation steers the model to output the attacker-chosen text and/or make the subsequent dialog follow the...

iPhone to Android (DeGoogled), whats it like?
Intro...
This Machine Could Keep Moore’s Law on Track (spectrum.ieee.org)

Instead of obtaining a warrant, the NSA would like to keep buying your data (arstechnica.com)

Room Temperature Superconductors - This Changes EVERYTHING! (youtu.be)

Ivanti Warns of Another Endpoint Manager Mobile Vulnerability Under Active Attack (thehackernews.com)

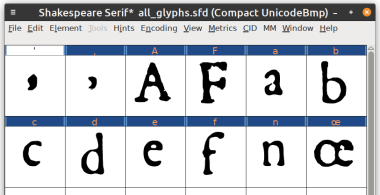
Shakespeare Serif - an experimental font based on the First Folio (shkspr.mobi)
I've built a new font! Thoughts and feedback on my approach very welcome.
ChatGPT broke the Turing test — the race is on for new ways to assess AI (www.nature.com)

Mark Zuckerberg: Threads users down by more than a half (www.bbc.com)

Cryptography may offer a solution to the massive AI-labeling problem (www.technologyreview.com)

Did Facebook fuel political polarization during the 2020 election? It’s complicated. (arstechnica.com)

Sci-Hub's Alexandra Elbakyan Receives EFF Award for Providing Access to Scientific Knowledge * TorrentFreak (torrentfreak.com)

Tor’s shadowy reputation will only end if we all use it | Engadget (www.engadget.com)
